Multi-factor authentication (MFA) is one of the simplest ways to protect your accounts and data from cyber criminals.
Here at Breakwater, we’ve helped hundreds of end-user’s setup multi-factor authentication. And here are some of the common myths we’ve been busting.
(If you want to know more about what MFA is before continuing, read our blog on MFA first here.)
#1 MFA is expensive 💰
When it comes to setting up MFA across an organisation, there will likely be costs involved from your IT provider to setup and support users. However, these are one-time setup fees and further support with MFA shouldn’t be required.
MFA applications, like the Microsoft Authenticator, are free to download and use. This means you can enable MFA on any of your accounts as you wish, absolutely ✨free!✨
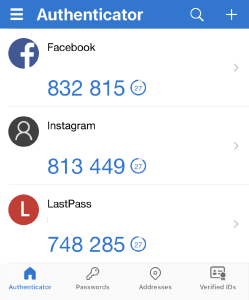
⬆️Microsoft Authenticator App
#2 I don’t have time to enable MFA ⏲️
Hey👋 we’re an IT provider and we can do it for you.
But, when it comes to individual applications, setting up MFA only takes a few minutes. Just head to your account privacy settings, open your MFA app and follow the steps.
Side note: even if it did take time to setup, it’s better than having your accounts hacked by cyber criminals…
#3 I don’t want to enter an MFA code every time I login
It can be frustrating when you’re trying to login and get on with work, and your MFA prompt stops you in your tracks.
But, it does only take a few moments. And once you get in the habit of entering it, you’ll have your phone ready to go before you login.
Bonus: Most MFA will allow you to recognise a device or browser. This means when you login to your accounts using the same device/browser, you won’t need to enter your MFA code every time.
#4 I don’t want to use my phone for MFA📱
We get that sometimes you may not want to use a personal mobile for work purposes. In this case, you can use alternative MFA methods, such as hardware tokens.
Once you start using MFA, it’ll just become another part of your login process (or not thanks to the bonus tip in #3). And, of course, when it comes to security, the time and money invested in these tools should always be weighed against the cost of a breach.
What is Multi-Factor Authentication (MFA)?
Multi-factor authentication (MFA) is an authentication method that requires two or more verification factors. This means that when you want to login to an account or a site, you’ll enter your password, and you’ll need to enter a secondary access key.
Is MFA the Same as 2FA?
2FA requires two verifications, whereas MFA requires two or more. The verification methods used can be the same.
What are some examples of MFA?
There are various verification methods that can be used for MFA. This includes passwords, fingerprint, facial recognition, MFA codes, token generators, keys, and more.







